You are currently focusing on the certification. Go to program dashboard.
Your All Access Pass subscription has been suspended. Please contact us to resolve this issue.
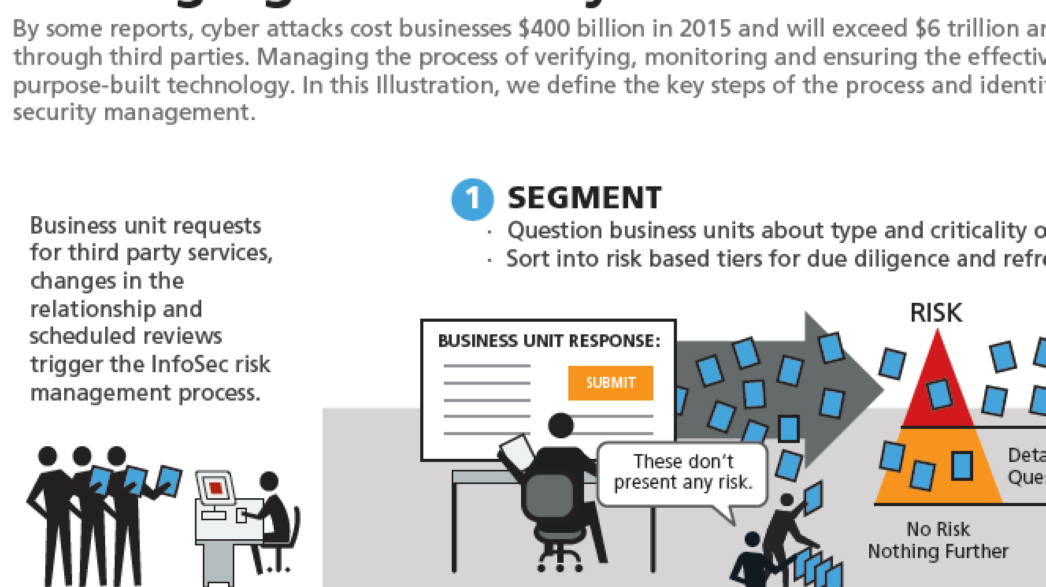
Information security is the risk topic of the year. In this Illustration we define the key steps of the process and identify what the future holds for third party information security management.
Despite incredible advances in technology and enhanced regulatory interest, the number of cyber-attacks involving access through third parties has grown dramatically. This isn’t surprising given that more than 80 percent of companies outsource some aspects of their business operations to third parties.
Managing the process of verifying, remediating where necessary and monitoring the effectiveness of third party controls demands the use of sophisticated and mission-designed technology. In this Illustration we define the key steps of the process and identify what the future holds for third party information security management.
Featured in: Third Party Management , Information Security
Like many websites, we use cookies and similar technologies such as session storage and analytics scripts to keep the site running smoothly and understand how visitors interact with our content. These tools may automatically collect technical information, including your device type, IP address, and browsing behavior.
By continuing to use this site, you acknowledge and accept this usage. For more information, please review our Terms of Service and Privacy Policy.
2942 N 24th St Ste 115 PMB 85352, Phoenix, AZ, 85016-7849, USA
Information & Billing
+1 (602) 234-9278
Principled Performance®, Driving Principled Performance®, Putting Principles Into Practice®, OCEG®, GRC360°®, ActiveLearning®, EventDay® and LeanGRC® are registered trademarks of OCEG®.
Protector Skillset™, Protector Mindset™, Protector Code™, Lines of Accountability™, GRC Professional™, GRCP™, GRC Fundamentals™, GRC Auditor™, GRCA™, GRC Audit Fundamentals™, Data Privacy Fundamentals™, Integrated Data Privacy Professional™, IDPP™, Policy Management Fundamentals™, Integrated Policy Management Professional™, IPMP™, Integrated Audit & Assurance Professional™, IAAP™, Integrated Governance & Oversight Professional™, IGOP™, Integrated Strategy & Performance Professional™, ISPP™, Integrated Risk Management Professional™, IRMP™, Integrated Decision Management Professional™, IDMP™, Integrated Compliance & Ethics Professional™, ICEP™, Integrated Business Continuity Professional™, IBCP™, Integrated Information Security Professional™, IISP™ are trademarks of OCEG®.

